When a ransomware attack hits, the clock starts ticking immediately. You might face encrypted files, a demanding note for payment, and a network that feels like it's falling apart. But panic doesn't help you recover data or stop the spread. Instead, you need a structured approach to Ransomware Forensics, which is the process of analyzing cryptographic keys, ransom notes, and attacker lateral movement to reconstruct events, support containment, and enable possible decryption. This isn't just about turning off servers; it's about understanding how the attackers moved, what they left behind, and whether your data can be restored without paying them.
In this guide, we break down the three pillars of ransomware investigation: recovering encryption keys from volatile memory, decoding the clues hidden in ransom notes, and mapping the lateral movement that allowed the attackers to compromise your entire network. We'll look at real-world techniques, specific tools, and the forensic artifacts you need to preserve before they disappear.
Key Recovery: The Race Against Volatility
The most critical window for ransomware forensics is often measured in minutes. Unlike traditional malware that leaves static files on disk, modern ransomware relies heavily on cryptography that exists primarily in memory. Once the encryption process finishes, the session keys used to lock your files are often wiped from RAM. If you wait too long, those keys are gone forever.
Historically, early ransomware like the 1989 AIDS Trojan used simple symmetric encryption that could be reversed by reverse-engineering the code. By 2013, families like CryptoLocker shifted to robust public-key cryptography, using RSA-2048 keys stored only on the attacker’s command-and-control (C2) infrastructure. Today, families like WannaCry, Ryuk, and REvil use a hybrid approach: AES-256 for fast file encryption and RSA-2048 or RSA-4096 to protect the session keys. This makes brute-forcing keys computationally infeasible with current hardware.
To recover these keys, investigators focus on Memory Forensics, which is the analysis of volatile computer memory (RAM) to find evidence such as encryption keys, running processes, and network connections that do not persist on disk. NIST Special Publication 800-86 emphasizes acquiring volatile memory immediately during incident response. Tools like the Volatility Framework, an open-source memory forensics tool used to analyze RAM dumps for cryptographic keys, malware artifacts, and system state information, are industry standards here. Analysts scan memory dumps for AES keys, key schedules, or known structures using YARA rules.
A notable success case occurred in 2016 with TeslaCrypt. The operators publicly released a master decryption key, allowing ESET to publish a free decryptor that restored files for thousands of victims without ransom payments. While this is rare, Europol’s "No More Ransom" project has helped over 6 million victims since 2016 by providing decryptors for families with implementation flaws or leaked keys. However, for properly implemented schemes, key recovery usually requires capturing the keys in memory before they are destroyed or identifying mistakes in key generation, such as poor entropy or reused RSA primes.
Analyzing Ransom Notes: More Than Just Demands
Ransom notes are not just extortion letters; they are rich forensic artifacts. Whether delivered as text files like "@[email protected]" in WannaCry or HTML pages changing your desktop wallpaper, these notes contain identifiers, infrastructure pointers, and campaign metadata that help attribute the attack and track its timeline.
A typical ransom note includes:
- Unique Victim ID: Usually a Base64 or hex string (16-64 characters) that links the victim to a specific decryption key on the attacker's end.
- Payment Instructions: Bitcoin or Monero addresses, Tor .onion URLs, or TOX IDs for communication.
- Deadlines: Often 3-7 days, after which the price increases or the data is threatened with deletion.
- Threats: Modern groups like Conti and LockBit often include links to leak sites, signaling a double-extortion tactic where stolen data is published if payment isn't made.
From a forensic perspective, ransom notes can be carved from disk, recovered from shadow copies, or correlated across multiple victims. Shared Bitcoin addresses or Tor URLs allow analysts to attribute attacks to specific groups. For example, blockchain analysis tools like Chainalysis Reactor can track payments and link seemingly unrelated incidents to the same criminal organization.
Timestamps on ransom note creation also aid in timeline reconstruction. In many campaigns, the ransomware binary writes notes to every directory after the lateral movement and encryption stages complete. By comparing creation times across systems, analysts can infer the order of deployment. Staggered timestamps over hours might indicate manual operator execution, while near-simultaneous timestamps within seconds suggest automated mass deployment via Group Policy or centralized management tools.

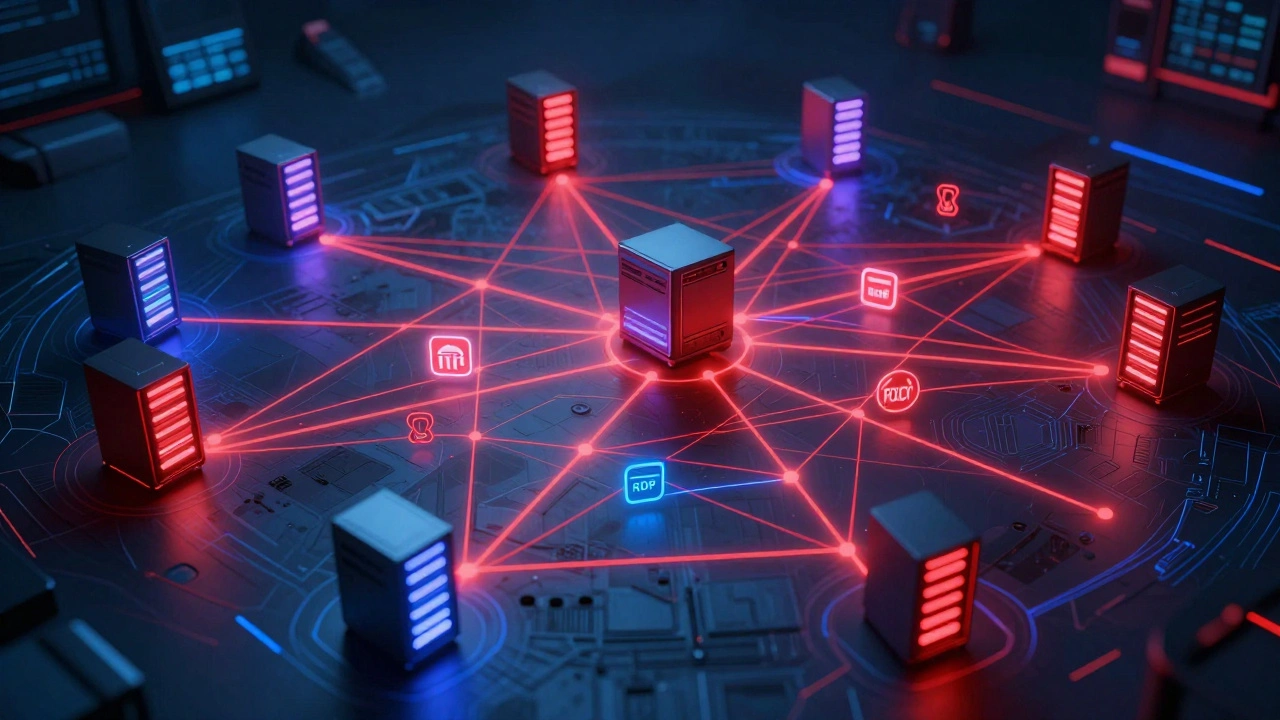
Mapping Lateral Movement: The Silent Spread
Lateral movement is the phase where adversaries move "east-west" across internal systems to reach high-value assets. It is often the most difficult stage to detect because it mimics normal administrative activity. According to Mandiant’s "M-Trends 2022" report, the median global dwell time for intrusions was 21 days, giving attackers ample time to probe networks before triggering encryption.
The MITRE ATT&CK framework documents numerous lateral movement techniques, including T1021 (Remote Services), T1078 (Valid Accounts), and T1028 (Windows Remote Management). Attackers commonly use tools like Cobalt Strike, Mimikatz, PsExec, and built-in Windows utilities to pivot across domains. For instance, the Yurei ransomware group uses Windows PSCredential objects, CIM sessions, and "net use" commands to propagate, closing sessions afterward to reduce artifacts.
To map lateral movement, forensic analysts correlate endpoint logs, authentication events, EDR telemetry, and network flows. Key Windows artifacts include:
- Security Log Event IDs: 4624/4625 (logon attempts), 4672 (special privileges), 4768/4769 (Kerberos tickets).
- Sysmon Event IDs: 1 (process creation) and 3 (network connections), configured to log detailed parent-child relationships.
- Active Directory Replication Logs: To detect unauthorized changes to user accounts or groups.
- RDP Connection Histories: To identify remote access from compromised endpoints.
Extended Detection and Response (XDR) platforms unify telemetry across endpoints, networks, and identities, enabling correlation rules like "new domain admin account created" followed by RDP sessions from a low-privilege workstation. This holistic view is crucial for detecting subtle privilege escalations that legacy SIEM tools might miss due to alert fatigue.
| Artifact Type | Primary Use | Volatility | Common Tools |
|---|---|---|---|
| Encryption Keys | Data Decryption | High (RAM) | Volatility, MemProcFS |
| Ransom Notes | Attribution & Timeline | Low (Disk) | File Carving, Shadow Copies |
| Event Logs | Lateral Movement Mapping | Medium (Syslog/SIEM) | Sysmon, Splunk, Elastic |
| Network Flows | C2 Communication | Low (PCAP) | Wireshark, Zeek |
Best Practices for Incident Response
Effective ransomware forensics starts immediately upon detection. SANS Institute courses like FOR528 recommend collecting RAM images within the first 1-2 hours of discovery. Preserve system logs for at least 30-90 days, as recommended by NIST SP 800-61r2. Use tools like KAPE (Kroll Artifact Parser and Extractor) and Velociraptor to extract keys and map lateral movement efficiently.
Collaboration is key. Share indicators of compromise (IOCs) with law enforcement and threat-intel partners. Organizations like CISA and the FBI provide joint advisories that help contextualize your findings within broader campaigns. Remember, forensic acquisition is not just about technical recovery; it supports legal actions and regulatory compliance, such as GDPR reporting requirements.
How quickly should I acquire memory after detecting ransomware?
Ideally within the first 1-2 hours. Encryption keys often exist in RAM only for minutes or hours before being wiped. Delaying acquisition significantly reduces the chance of key recovery.
Can ransomware always be decrypted without paying?
No. Reliable key recovery is only feasible in a minority of cases, typically when attackers make implementation errors or leak keys. For robust AES-256/RSA-2048 schemes, brute-forcing is computationally infeasible. Always check No More Ransom for available decryptors first.
What are the most important Windows event IDs for lateral movement?
Focus on Security log IDs 4624/4625 (logons), 4672 (special privileges), and 4768/4769 (Kerberos tickets). Sysmon IDs 1 (process creation) and 3 (network connections) are also critical for mapping process chains and network hops.
Why are ransom notes useful for forensics?
They contain unique victim IDs, payment addresses, and deadlines that help attribute attacks to specific groups. Timestamps on note creation also reveal whether deployment was manual or automated, aiding timeline reconstruction.
How does XDR improve ransomware detection?
XDR unifies telemetry from endpoints, networks, and identities, allowing correlation of subtle events like new admin accounts followed by unusual RDP sessions. This helps detect lateral movement that legacy SIEM tools might miss due to high alert volumes.





