Imagine sending a contract across the globe, only to have it rejected in court because the signature wasn't "real." It sounds like a scene from a bad legal drama, but for decades, this was a genuine risk. Today, that fear is largely obsolete. Digital signatures are cryptographically-based electronic authentication mechanisms that use public key infrastructure (PKI) to verify identity and document integrity. As of May 2026, these tools are legally recognized in over 180 countries. But recognition isn't the same as automatic validation. The real question isn't just whether a digital signature is legal-it's whether it holds up under scrutiny when disputes arise.
The shift from ink to bits has transformed how we handle agreements, but it hasn't eliminated the need for proof. In fact, it has made the concept of chain of custody more critical than ever. You can't physically hand a paper document to a judge; you must prove that the digital file you present is the exact same file that was signed, unaltered, and stored securely. This article breaks down where digital signatures are accepted, how they are validated, and why the technical details matter just as much as the legal ones.
How Digital Signatures Work Technically
To understand why courts accept them, you first need to know what makes a digital signature different from a scanned image of a handwritten name. A simple image can be copied and pasted anywhere. A true digital signature is tied to the specific document and the specific signer using mathematics.
This process relies on Public Key Infrastructure (PKI), a system based on asymmetric cryptography. When you sign a document, your software uses a private key-kept secret by you-to create a unique mathematical hash of the document. This hash is then encrypted with your private key to form the signature. Anyone with your public key can decrypt the signature and compare the resulting hash to the current hash of the document. If even one character in the document changes after signing, the hashes won't match, and the signature becomes invalid.
This mechanism provides two crucial benefits:
- Non-repudiation: The signer cannot deny signing the document because only their private key could have created that specific signature.
- Integrity: The document cannot be altered without breaking the signature, providing a built-in tamper-evident seal.
For forensic analysis or legal defense, this cryptographic link is the foundation of trust. Without it, you're just arguing about who clicked a button.
Global Legal Frameworks and Acceptance
Legal acceptance varies significantly depending on where the transaction takes place. While most developed nations recognize digital signatures, the level of protection they offer differs. Understanding these tiers helps you choose the right tool for the job.
| Sigature Tier | Technical Requirements | Legal Presumption | Common Use Cases |
|---|---|---|---|
| Simple Electronic Signature | Basic identification (e.g., email address, checkbox) | Low; burden of proof is on the signer | Internal memos, low-risk NDAs |
| Advanced Electronic Signature | Unique link to signer, detectable alterations, exclusive control of signing data | Moderate; admissible as evidence | B2B contracts, HR documents |
| Qualified Electronic Signature (QES) | Government-certified certificate, secure hardware token, timestamping | High; equivalent to handwritten signature in many jurisdictions | Real estate, government filings, high-value transactions |
North America: ESIGN and UETA
In the United States, the Electronic Signatures in Global and National Commerce Act (ESIGN) and the Uniform Electronic Transactions Act (UETA) provide the legal backbone. These laws state that a record or signature may not be denied legal effect solely because it is electronic. However, they do not mandate a specific technology. This means a click-wrap agreement is valid, but so is a PKI-based signature. The catch? If a dispute arises, you must prove that the signature was indeed yours and that the document wasn't changed. For high-stakes litigation, simpler methods often fail this test without extensive audit logs.
Canada follows a similar path under PIPEDA, recognizing digital signatures as legally binding. Mexico, however, requires more rigor under its Advanced Electronic Signature Law, mandating that signature creation data remains under the exclusive control of the signatory and that any post-signature alteration is detectable.
Europe: The eIDAS Standard
The European Union operates under Regulation (EU) No. 910/2014, known as eIDAS. This regulation is stricter and more structured than US law. Article 25(i) explicitly states that an electronic signature shall not be denied legal effect solely because it is electronic. More importantly, eIDAS creates a presumption of validity for Qualified Electronic Signatures (QES). If you use a QES issued by a trusted service provider within the EU, the burden of proof shifts to the party challenging the signature. This is a massive advantage in cross-border trade within Europe.
Countries like Spain, Germany, and Ireland have aligned their national laws with eIDAS, granting full legal validity to electronic signatures for most agreements. Switzerland, while not in the EU, permits electronic signatures when parties agree, mirroring the flexibility seen in other parts of Europe.
Asia-Pacific: Diverse Approaches
The Asia-Pacific region presents a complex patchwork. India’s Information Technology Act 2000 distinguishes between general electronic signatures and digital signatures using certificates from licensed authorities. Crucially, India excludes contracts involving immovable property, negotiable instruments, and powers of attorney from electronic execution entirely.
China’s Electronic Signature Law recognizes e-signatures if both parties consent, but courts heavily favor "reliable" signatures with verified identity and timestamping. Traditional seals (chops) still dominate in government filings and land transfers. Japan has moved away from its traditional hanko seal culture, especially post-pandemic, granting electronic signatures the same presumption of authenticity as sealed documents when technical criteria are met.

Chain of Custody in the Digital Age
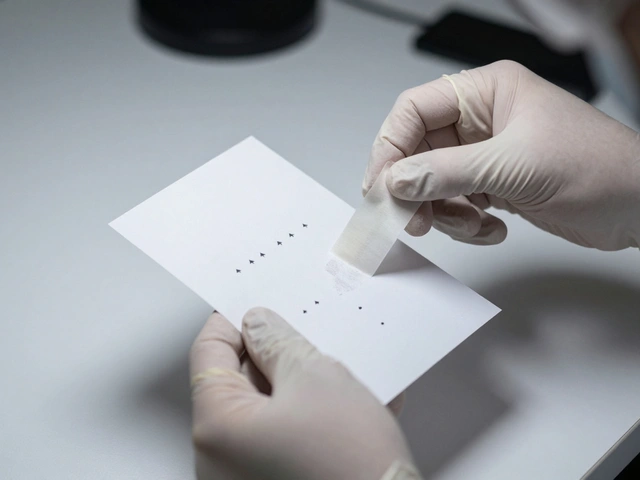
In physical forensics, chain of custody tracks every person who handled a piece of evidence. In the digital world, this concept translates to audit trails and metadata verification. A digital signature alone is not enough; you need to prove the journey of the document from creation to storage.
A robust chain of custody for digital signatures includes:
- Identity Verification: How did the platform confirm the signer's identity? Was it via SMS, video KYC, or government ID?
- Timestamping: Trusted Timestamp Authorities (TSA) embed a cryptographically secure time record. This proves the document existed in its signed state at a specific moment, preventing backdating or forward-dating disputes.
- Access Logs: Who opened the document? When? From which IP address? Detailed logs prevent claims of unauthorized access.
- Hash Integrity Checks: Regular verification that the document's hash matches the original signed hash ensures no silent alterations occurred during storage.
Without these elements, a digital signature is just a static attachment. With them, it becomes a defensible record of truth. For legal teams and forensic analysts, this metadata is often more valuable than the signature itself.
Cross-Border Validation Challenges
Doing business internationally introduces friction. Just because a signature is valid in the US doesn't mean it's automatically enforceable in Brazil or Thailand. Cross-border validation requires careful planning.
The EU-Japan Economic Partnership Agreement, for example, includes clauses facilitating electronic signature usage between parties in those jurisdictions. Mutual recognition agreements help, but they aren't universal. Foreign businesses operating in China, for instance, must explicitly confirm with counterparts that e-signed contracts will be accepted in court. Relying on assumption is a recipe for costly litigation.
Key strategies for cross-border success include:
- Explicit Consent Clauses: Include language in the contract stating that both parties agree to the use of digital signatures and specify the governing law.
- Use Qualified Signatures: When dealing with regulated industries or high-value transactions, opt for QES or equivalent local standards to maximize legal protection.
- Localize Storage: Some jurisdictions require data residency. Ensure your document storage complies with local privacy laws like GDPR or China's PIPL.
Future Trends: Quantum Resistance and Blockchain
The landscape is evolving rapidly. By 2026-2028, the threat of quantum computing to current PKI algorithms (like RSA) will become a serious concern. NIST Post-Quantum Cryptography standards, finalized in August 2022, are guiding the migration toward quantum-resistant algorithms. Organizations relying on long-term document retention must plan for this transition now.
Additionally, blockchain-based timestamping is emerging as an alternative to traditional centralized Trust Service Providers. Distributed ledger technology offers immutable proof of existence without relying on a single authority. While regulatory acceptance is still developing, early adopters are leveraging blockchain for enhanced transparency in supply chain contracts and intellectual property rights.
Central Bank Digital Currencies (CBDCs) also present new opportunities. Integrating digital signatures with programmable payments could automate contract execution, reducing the need for manual validation steps entirely.
Are digital signatures legally binding in all countries?
No, not universally. While over 180 countries recognize electronic signatures, the level of legal validity varies. Some countries, like India and China, exclude specific types of contracts (such as real estate or inheritance) from digital execution. Always check local regulations before relying on digital signatures for high-stakes transactions.
What is the difference between an electronic signature and a digital signature?
An electronic signature is a broad term encompassing any electronic method of signing, including a typed name or checkbox. A digital signature is a specific type of electronic signature that uses PKI cryptography to verify identity and ensure document integrity. Digital signatures offer higher security and legal presumptions in many jurisdictions.
How do I maintain a proper chain of custody for digital documents?
Maintain detailed audit trails that include identity verification records, timestamps from trusted authorities, access logs showing who viewed or modified the document, and regular hash integrity checks. Using platforms that provide comprehensive reporting features is essential for forensic defensibility.
Is a Qualified Electronic Signature (QES) always required?
Not always. For most B2B contracts and internal documents, advanced electronic signatures are sufficient. QES is typically required for high-value transactions, government filings, or in jurisdictions like the EU where specific legal presumptions are needed for certain types of agreements.
What happens if a digital certificate expires?
If a certificate expires after signing, the signature usually remains valid as long as the certificate was active at the time of signing. However, some systems may flag expired certificates during verification. It is best practice to use timestamping to lock in the validity status at the moment of signing, ensuring long-term enforceability.