Imagine a judge staring at a photo on a screen. The defense attorney stands up and asks, "How do we know this image wasn't edited after it was taken?" That single question hangs in the air. If you cannot prove that the file is exactly what it was when collected, your case might crumble. This is the core challenge of digital evidence, which is information stored or transmitted in binary form that may be relied upon in court. Unlike a physical bullet or a bloodstain, digital files can be altered without leaving visible traces. To protect your case, you need two things: proof of authenticity and an unbroken chain of custody.
What Is Digital Evidence Authenticity?
Authenticity answers one simple question: Is this file what the proponent claims it is? In the United States, Federal Rule of Evidence 901 requires that the proponent produce evidence sufficient to support a finding that the item is what the proponent claims. Courts generally presume digital evidence is authentic unless the opposing party raises a specific challenge. When they do, the burden shifts to you to show reliability.
In Europe, the rules are slightly different but equally strict. Under Regulation (EU) No 910/2014, also known as eIDAS, a qualified electronic signature has the same legal effect as a handwritten signature. Article 35 states that qualified electronic seals enjoy a presumption of integrity and correctness of origin. This means if you use a compliant digital seal, the court assumes the data hasn't changed unless someone proves otherwise.
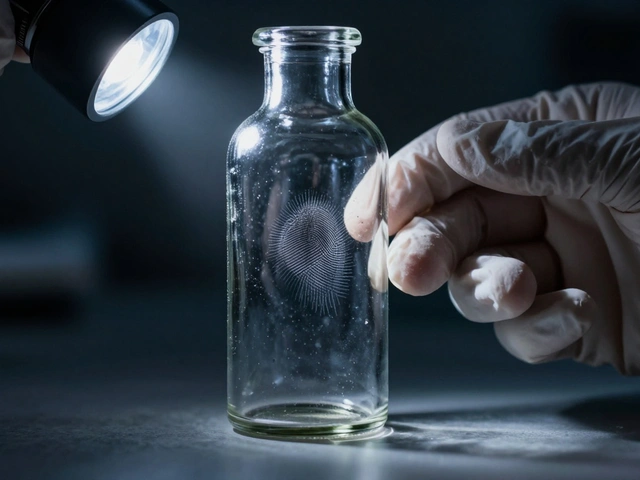
Technically, authenticity relies on cryptographic controls. A cryptographic hash acts as a digital fingerprint computed at creation, where any bit-level change produces a different hash value. Standards like SHA-256, defined by NIST in FIPS PUB 180-4, generate a unique 256-bit string for every file. If the hash calculated at acquisition matches the hash recalculated later, you have strong technical proof that the file was not modified.
The Chain of Custody Explained
If authenticity proves the file is genuine, the chain of custody proves it wasn't tampered with while in your possession. It is the documented, chronological record of every handoff, analysis, and storage event. According to ISO/IEC 27037:2012, guidelines for identification, collection, acquisition and preservation of digital evidence, every transfer must be documented with the responsible person, date, and conditions.
A proper log must answer four key questions:
- Who collected or accessed the evidence?
- When and where was it collected or transferred?
- What actions were taken on the data?
- How was it stored or secured?
Any break in this chain-like a missing signature or an undocumented gap-can lead to exclusion. Judges look for auditability, meaning an independent third party should be able to reconstruct each step. They also look for repeatability, ensuring the same procedures yield identical results, and justifiability, where every action follows recognized methodologies.

Technical Controls for Integrity
You cannot rely on paperwork alone. Technical safeguards are essential to maintain integrity from seizure to courtroom presentation. Here are the primary tools used in modern forensics:
| Mechanism | Function | Standard/Protocol |
|---|---|---|
| Cryptographic Hash | Verifies file content has not changed | SHA-256 (FIPS PUB 180-4) |
| Digital Signature | Confirms signer identity and integrity | NIST FIPS 186-4 |
| Trusted Timestamp | Proves existence at a specific time | RFC 3161 (IETF) |
| Write Blockers | Prevents alteration during acquisition | Hardware/Software Enforcement |
Using write-blocking hardware or software ensures you don't accidentally modify the original drive while imaging it. You should always work on forensic copies, preserving the original as a master copy. Tools like FTK Imager or EnCase Forensic automatically log these operations, creating machine-generated audit trails that are far more reliable than manual notes.

Best Practices for Handling Evidence
Human error remains the biggest threat to chain of custody. Forgetting to sign a form or mislabeling a drive can destroy months of work. To avoid this, agencies are moving toward Digital Evidence Management Systems (DEMS) like Axon Evidence or NICE Investigate. These platforms replace paper forms with automated logging, assigning unique identifiers such as barcodes plus digital hash values to each item.
Key operational steps include:
- Use tamper-evident packaging for physical media.
- Implement role-based access controls in storage vaults.
- Train personnel regularly on standard operating procedures (SOPs).
- Review SOPs at least annually to adapt to new technologies.
Emerging technologies like blockchain are being explored to anchor hash values into distributed ledgers. This makes subsequent tampering detectable because the blockchain-stored hash will no longer match the current file. While still emerging, this approach adds a layer of immutability that traditional databases lack.
Legal Presumptions and Burdens
Understanding where the burden of proof lies is crucial. In most U.S. federal courts, under Federal Rules of Evidence 901 and 902, digital evidence is presumed authentic unless challenged. However, amendments in 2017 added Rules 902(13) and 902(14), allowing certain certified records generated by electronic processes to be self-authenticating. This reduces the need for live testimony about chain of custody when specific technical conditions are met.
In Germany, §371a of the Zivilprozessordnung (ZPO) creates a similar presumption for electronic documents with qualified signatures. In England and Wales, Civil Procedure Rules Part 31 and ACPO principles require an audit trail that allows independent examination. Regardless of jurisdiction, the goal is the same: assure the judicial authority that the evidence presented is the same as what was seized.
What happens if the chain of custody is broken?
If the chain of custody is broken, the opposing party can argue that the evidence was tampered with or contaminated. This often leads to the evidence being excluded from trial or given less weight by the jury. Even a single undocumented transfer can raise reasonable doubt about integrity.
Is a cryptographic hash enough to prove authenticity?
A cryptographic hash proves that the file has not changed since the hash was created. However, it does not prove who created the original file or when. To fully establish authenticity, you typically need to combine hashing with digital signatures, trusted timestamps, and a documented chain of custody.
What is ISO/IEC 27037?
ISO/IEC 27037 is an international standard that provides guidelines for the identification, collection, acquisition, and preservation of digital evidence. It sets out requirements for maintaining integrity and chain of custody, emphasizing auditability, repeatability, and justifiability in forensic processes.
Why should I use a Digital Evidence Management System (DEMS)?
A DEMS automates the logging of evidence handling, reducing human error. It assigns unique identifiers, tracks access with precise timestamps, and centralizes storage with permission-based visibility. This automation creates a robust audit trail that is much harder to challenge in court than manual paper logs.
How does eIDAS affect digital evidence in Europe?
eIDAS Regulation gives qualified electronic signatures and seals the equivalent legal effect of handwritten signatures and presumptions of integrity. This means that if you use a qualified trust service provider to sign or seal digital evidence, European courts must presume its authenticity and origin unless proven otherwise.