You collect a sample. You seal it in a bag. You label it. You think you’re done. But if you can’t prove exactly who held that bag, where it sat, and what temperature it experienced between collection and analysis, your evidence is worthless. In legal proceedings, regulatory audits, or quality control investigations, the story matters just as much as the substance. That story is told through chain of custody documentation and strict adherence to storage conditions.
Chain of custody isn’t just paperwork; it’s the backbone of credibility. It tracks every handoff, every storage event, and every access point from the moment evidence leaves its source until it reaches final disposition. Without this unbroken trail, questions arise about tampering, contamination, or misidentification. And once those questions appear, the integrity of your case-or your product-crumbles.
What Is Chain of Custody?
Chain of custody is a systematic tracking mechanism that documents the sequential control, transfer, analysis, and disposition of evidence or products from point of origin to final destination. Think of it as a digital or physical ledger that never sleeps. Every time someone touches the item, moves it, stores it, or analyzes it, they leave a mark on that ledger.
This process serves three critical purposes:
- It allows analytical laboratories to be questioned specifically about how evidence was handled before arrival.
- It maintains an official, auditable record of who had control at any given time.
- It proves that only approved personnel accessed the sample and that it remained protected from tampering.
If even one link in this chain is weak or missing, the entire structure becomes vulnerable to challenge. In court, a broken chain can mean dismissed evidence. In industry, it can mean failed compliance audits or rejected shipments.
The Starting Point: Origin Documentation
The chain begins at the point of origin. This could be a farm, a manufacturing plant, a crime scene, or a server room. Whatever the location, the first record sets the tone for everything that follows. If the initial data is sloppy, every subsequent entry inherits that error.
At this stage, you need to capture specific details:
- Source location and facility name: Where exactly did this come from?
- Date and time of receipt or production: Precision matters down to the minute.
- Amount and quality characteristics: Weight, volume, grade, purity, or condition.
- Identity of the initial owner or custodian: Who is responsible right now?
These facts form the foundation. Later investigators or auditors will trace back to this moment to verify authenticity. Make sure this first entry is accurate, complete, and signed by the person taking initial custody.
Essential Components of Chain of Custody Documentation
A proper chain of custody document isn’t a simple log sheet. It’s a comprehensive record that answers every possible question about the item’s journey. Here’s what must be included:
| Field | Description |
|---|---|
| Name and signature of collector | Who gathered the sample and verified its initial state? |
| Official address and contact number | How can the collecting party be reached for verification? |
| Name of recipient | Who accepted responsibility next? |
| Laboratory or storage facility address | Where is the item currently located? |
| Unique identifier for each sample | Barcode, serial number, or case-specific ID to prevent mix-ups. |
| Matrix type | Blood, soil, software code, financial records-what kind of evidence is this? |
| Date and time of collection | Exact timestamp when possession began. |
| Type of analysis required | DNA testing, chemical assay, code review? Specify the intent. |
| Signatures of all handlers | Every person who takes custody must sign with date and time. |
| Date and method of delivery | Was it shipped via courier, carried internally, transferred digitally? |
| Authorization for analysis | Who approved the next step? Include names and titles. |
For document storage specifically, add these fields:
- Name of the person accessing the document
- Date, time, and place of access
- Name of the storage employee assisting (if applicable)
- Description of the document accessed and data obtained
Missing any of these creates gaps. Gaps invite suspicion. Suspicion kills credibility.

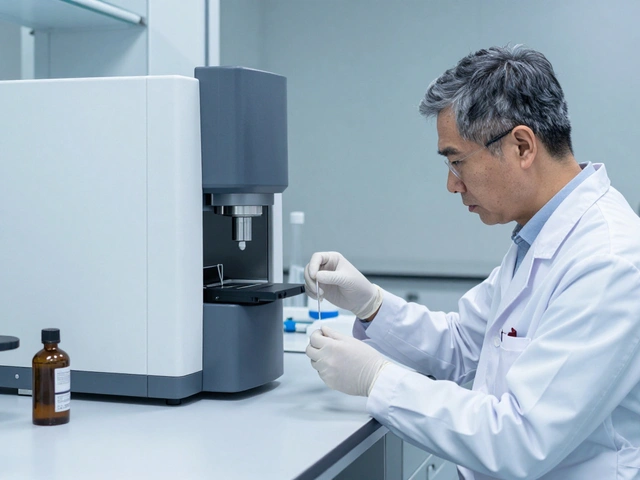
Storage Conditions: The Silent Guardian
Documentation tells the story, but storage conditions protect the truth. Samples degrade, documents get damaged, and digital files corrupt. If the environment isn’t controlled, the evidence itself changes-and no amount of paperwork can fix that.
Whenever samples are not under direct control, they must be kept in secured locations:
- Locked vehicles: For transport between sites.
- Locked refrigerators or freezers: For biological or perishable samples.
- Locked laboratories with limited access: For ongoing analysis.
- Climate-controlled vaults: For sensitive documents or archival materials.
Access control records must show every instance when someone entered the storage area. What did they do? How long were they there? Did they open any containers? These logs should be automated where possible, using badge swipes, camera footage, or digital audit trails.
For digital evidence, storage means more than hard drives. It includes:
- Backup procedures to prevent data loss
- Integrity monitoring via hash values
- Retention policies aligned with legal requirements
- Encryption to prevent unauthorized modification
Environmental controls matter here too. Server rooms need stable temperatures and humidity levels. Power fluctuations can corrupt files. Unplanned outages can erase logs. Documenting these conditions proves you took reasonable steps to preserve integrity.
Transfer Procedures: Keeping the Chain Intact
Transfers are where chains break most often. Moving evidence from one handler to another introduces risk. Each transfer must establish four things clearly:
- Who had responsibility before the transfer?
- Who took responsibility after?
- When and where did the handover occur?
- Under what circumstances was the transfer made?
This applies to physical items, digital files, and even system migrations. If you move evidence from one server to another, that’s a transfer. If you grant temporary access to a third-party analyst, that’s a transfer. Every change in custody needs documentation.
Best practices include:
- Requiring signatures or digital acknowledgments from both parties.
- Recording the reason for the transfer (e.g., “for DNA analysis” or “archival backup”).
- Noting the destination location and transport method.
- Listing security measures applied during transit (sealed container, GPS tracking, encrypted upload).
Transportation companies become temporary custodians. Their vehicles, drivers, and procedures become part of your chain. Vet them carefully. Check their background check frequency, vehicle security, and emergency response plans.

Implementing Chain of Custody Systems
You don’t need fancy software to start. A well-designed log works. But consistency is key. Every time someone has custody, a notation must be made. No exceptions. No “I’ll fill it out later.” Delayed entries create ambiguity.
Start by identifying:
- Types of sensitive information you handle
- Current storage locations
- Who currently has access
- Existing policies around retrieval and movement
Create a standard form. Use barcodes or QR codes for quick scanning. Train staff on why accuracy matters-not just because “it’s policy,” but because mistakes have real consequences.
Consider service providers if you lack internal capacity. Evaluate them on:
- Vehicle security and tracking capabilities
- Employee screening processes
- Storage environment controls (temperature, humidity, fire suppression)
- Monitoring systems (cameras, alarms, access logs)
- Tracking devices used (barcode labels, RFID tags)
- Emergency retrieval options
- Willingness to sign non-disclosure agreements
Don’t assume professionalism equals competence. Ask for proof. Request sample logs. Test their response times.
Digital Evidence: Special Considerations
Digital evidence behaves differently than physical samples. It doesn’t rot, but it can be altered without a trace. Hash values are your best friend here. Generate a checksum at collection. Verify it at every transfer. Any change breaks the chain.
DevSecOps teams should record:
- Timestamps of collection and access
- Hash values of files and directories
- Environmental conditions during collection (network status, user activity)
- Tools used for imaging or copying
Evidence types include:
- Source code repositories
- Container images
- Configuration files
- System logs
Each piece needs unique identification. Digital signatures help. Automated systems assist, but human oversight remains essential. Algorithms miss context. Humans catch anomalies.
Why This Matters More Than Ever
In today’s world, scrutiny is higher. Regulatory bodies demand transparency. Courts require verifiable trails. Customers expect accountability. Your chain of custody isn’t just a procedural requirement-it’s a competitive advantage.
Proper documentation ensures:
- Traceability from origin to outcome
- Prevention of unauthorized alterations
- Accountability for every individual involved
- A verifiable record for legal or audit purposes
- Maintenance of evidence integrity throughout its lifecycle
When things go wrong-and they will-you’ll thank yourself for keeping meticulous records. When things go right, you’ll still need them to prove it.
What happens if the chain of custody is broken?
A broken chain of custody undermines the credibility of the evidence. In legal contexts, it may lead to exclusion of evidence from trial. In commercial settings, it can result in failed audits, rejected claims, or loss of customer trust. Once integrity is questioned, rebuilding confidence requires significant effort and often cannot fully restore original standing.
Can digital tools replace manual chain of custody logs?
Digital tools enhance accuracy and speed but don’t eliminate the need for human oversight. Automated systems can track timestamps, generate hashes, and log accesses, but they rely on correct configuration and regular validation. Human review ensures contextual understanding and catches errors machines might miss. Best practice combines automation with periodic manual audits.
How long should chain of custody records be retained?
Retention periods depend on jurisdiction and industry regulations. Generally, keep records for at least seven years for legal cases, ten for environmental or health-related evidence, and indefinitely for criminal convictions. Always consult local laws and organizational policies. Store backups securely and ensure accessibility for future verification.
Who is responsible for maintaining the chain of custody?
Responsibility lies with whoever currently holds custody. Each person must document their actions and formally transfer responsibility to the next handler. Organizations should assign overall accountability to a designated manager or compliance officer who oversees training, audits, and system maintenance. Shared responsibility prevents gaps.
What are common mistakes in chain of custody documentation?
Common errors include incomplete signatures, missing timestamps, vague descriptions of transfers, failure to note environmental conditions, and delayed logging. Another frequent issue is assuming informal handoffs don’t require documentation. Even brief exchanges must be recorded. Consistency and attention to detail prevent costly oversights.
Does chain of custody apply to non-physical evidence like emails or databases?
Yes. Digital evidence requires equally rigorous tracking. Record creation dates, modification histories, access logs, and encryption statuses. Use hash verification to confirm file integrity. Treat email threads, database exports, and cloud storage snapshots as tangible assets needing protection and documentation.
How do I train staff on proper chain of custody procedures?
Training should cover the importance of accuracy, step-by-step documentation processes, recognition of potential risks, and consequences of errors. Use real-world examples and role-playing exercises. Conduct regular refresher courses and surprise audits to reinforce habits. Provide clear templates and digital tools to reduce friction in daily tasks.
What role does technology play in modern chain of custody management?
Technology enables faster, more accurate tracking through barcode scanners, RFID tags, blockchain ledgers, and automated logging systems. Cloud platforms allow remote access and real-time updates. However, tech solutions must be paired with strong governance frameworks. Tools support humans-they don’t replace judgment or accountability.