Imagine standing in a courtroom two years after a crime occurred. The opposing counsel points to a hard drive and asks, "How do we know this wasn't tampered with while it sat in your office for six months?" If you can't answer that with a precise, signed paper trail, your evidence-and potentially your entire case-could be thrown out. This is where chain of custody documentation is the chronological paper trail that records the sequence of custody, control, transfer, analysis, and disposition of physical or electronic evidence. It isn't just a bureaucratic formality; it is the only way to prove the legal integrity and authenticity of evidence before a judge or jury.
What Actually Goes Into a Chain of Custody Record?
A common mistake is thinking a simple note saying "collected by Officer Smith" is enough. In reality, for evidence to hold up under scrutiny, the documentation must be exhaustive. You need to capture every single touchpoint from the moment an item is seized until it is either destroyed or archived.
Every entry in your report should include these concrete details:
- The Who: Names of every investigator, technician, or courier who handled the item.
- The When: Exact dates and timestamps for collection, every transfer, and final disposition.
- The Where: Precise location of collection and specific storage details, such as a locker number or a secure server ID.
- The What: Detailed descriptions of the media. For a hard drive, don't just write "hard drive." Include the make, model, serial number, and total storage capacity.
- The How: The method of transport-was it a sealed evidence bag, an encrypted drive, or a secure courier?
If you are dealing with Digital Forensics, you must also include a unique identifier, like a cryptographic hash value (checksum), to prove that not a single bit of data changed during the process.
The Lifecycle of Evidence: From Scene to Court
To keep your reports bulletproof, you have to treat the chain of custody as a living document that follows a strict lifecycle. Any gap in this timeline is a "custody break," and that's where defense attorneys find their opening.
Step 1: Collection and Identification
The process starts the second you identify a piece of evidence. You must document the reason for collection and the exact environmental conditions. In a DevSecOps environment, this might mean recording system timestamps and the state of the network when a log was captured. The goal here is to establish a baseline of authenticity.
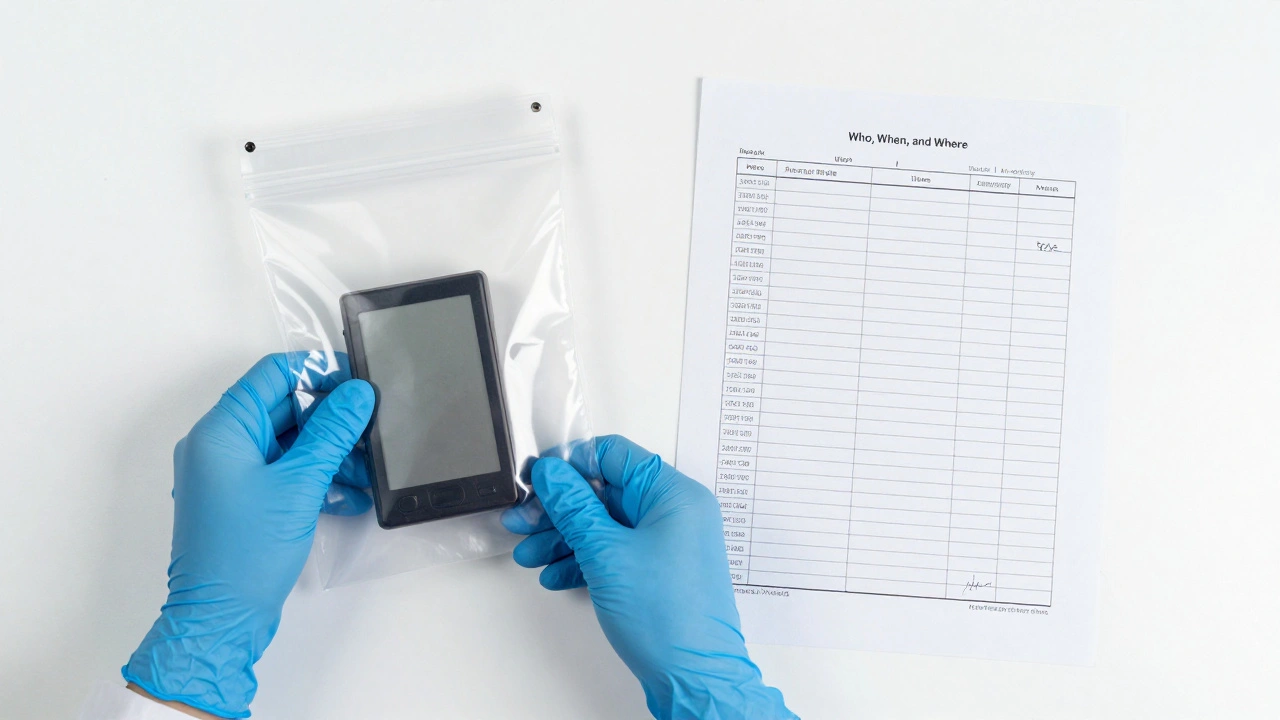
Step 2: Secure Transfer
Whenever evidence moves from person A to person B, it's a critical vulnerability point. A proper transfer requires a "hand-off" signature from both the transferring and receiving parties. Your report should specify why the transfer happened-for example, moving a sample from the field to a laboratory for chemical analysis.
Step 3: Storage and Access Control
Storage isn't just about putting things in a room; it's about documenting who has the key. You need records of who accessed the evidence, what they did with it (e.g., "extracted data for redaction"), and how long they had it. Laboratories must limit the number of people in contact with the evidence to keep the chain as short and clean as possible.
Step 4: Final Disposition
The chain doesn't end when the trial does. You must document the final destination of the evidence-whether it was returned to the owner, moved to a long-term archive, or destroyed according to legal protocols.
| Attribute | Physical Evidence | Digital Evidence |
|---|---|---|
| Verification Method | Tamper-evident seals / Signatures | Hash values (SHA-256/MD5) |
| Storage Detail | Locker number / Evidence room | Server ID / Encrypted Volume |
| Transfer Record | Physical logbook signature | Digital audit trail / API logs |
| Risk Factor | Physical contamination / Theft | Data corruption / Unauthorized access |
Handling Digital Evidence and Immutable Audit Trails
Digital evidence is trickier because it can be copied or altered without leaving a physical trace. To solve this, modern forensic reporting relies on immutable audit trails. These are logs that cannot be changed or deleted, providing a definitive reconstruction of events.
In high-end enterprise systems, like Salesforce, this is handled through specialized logging tools. For instance, a Setup Audit Trail tracks every administrative change, while Event Monitoring provides granular data on who executed a report or exported data. If a custody gap is suspected, security teams can use these logs to determine if a policy violation occurred. This creates a "meta-documentation" layer that proves the organization's commitment to integrity.
The Legal Consequences of Poor Documentation
Why spend so much time on this? Because the National Institute of Justice (NIJ) and the National Institute of Standards and Technology (NIST) make it clear: if you can't prove the chain, the evidence is compromised.
If a misstep occurs and isn't documented, the court may issue a "limiting instruction." This tells the jury to give less weight to the testimony because the evidence's authenticity is questionable. In the worst cases, the evidence is excluded entirely. If that hard drive was the only piece of proof linking a suspect to a crime, the case could collapse. Organizations that ignore these standards risk not only losing cases but also facing steep penalties and a total loss of public trust.
Application Across Different Industries
While we often think of police work, the principles of custody apply everywhere. In the pharmaceutical industry, documenting the chain of custody for medical specimens ensures that a patient's results aren't swapped. In supply chain management, it's used to prove that wood products come from sustainably managed forests or that food items haven't been contaminated during transit.
Even professional athletes face this. During drug testing, the chain of custody for a urine or blood sample is the only thing preventing an athlete from claiming the sample was switched or tainted. Whether it's a blood vial or a server log, the rule remains: if it wasn't documented, it didn't happen.
What happens if there is a gap in the chain of custody?
A gap, or "break," in the chain of custody means there is a period where the evidence's location or handler is unaccounted for. Legally, this can lead to the evidence being ruled inadmissible because the prosecution cannot prove it wasn't tampered with. In some cases, the judge may allow the evidence but instruct the jury to view it with skepticism.
Is a digital signature sufficient for a transfer record?
Yes, provided the digital signature is backed by a secure, time-stamped audit trail. In digital forensics, an electronic acknowledgment that is logged in an immutable system is often more reliable than a physical signature, as it provides an exact millisecond timestamp and verifies the identity of the user through authentication.
Do I need to document every single time I look at the evidence?
Yes. Every instance of access must be recorded. You should note the date, the time, the purpose of the access (e.g., "performing keyword search for evidence"), and the duration of the access. This prevents any claims that unauthorized modifications were made during the analysis phase.
What is the difference between a checksum and a chain of custody?
A checksum (or hash) proves that the content of a file has not changed. The chain of custody proves that the handling of the file was secure. You need both: the checksum proves the data is original, and the chain of custody proves who had access to that data and where it was kept.
How should I document the final disposition of evidence?
The final disposition should be the last entry in your chain of custody report. It must state exactly what happened to the item-for example, "Returned to owner on 2026-04-29 via certified mail" or "Destroyed by incineration per Court Order #123." Include the signature of the person performing the disposition and any witnesses present.