Before any piece of evidence can be shown to a jury, it must pass one critical gate: evidence authentication. This isn’t about proving something is true. It’s about proving it’s what the prosecutor or defense says it is. A photo of a weapon. A text message. A bag of powder. A signed contract. None of these can be admitted unless someone can show, with enough evidence, that it’s real and matches the claim being made.
Think of it like this: if you walk into court with a USB drive and say, "This contains the suspect’s confession," the judge doesn’t automatically accept it. You have to show how you know it’s really his confession-not someone else’s, not a fake, not altered. That’s authentication. It’s the first hurdle. And it’s lower than you think.
What Does Authentication Actually Require?
The bar isn’t high. You don’t need to prove beyond a doubt that the evidence is genuine. You only need to show enough to let a reasonable person believe it’s likely what you say it is. That’s called a prima facie showing. Once that’s done, the evidence goes to the jury. The jury then decides whether it’s truly authentic and how much weight to give it.
This rule applies everywhere-federal courts, state courts, military courts. Whether you’re in North Carolina, Massachusetts, or Wisconsin, the logic is the same: if you can’t show the item is what you claim, it doesn’t get in. But if you can, even just barely, it’s allowed.
How Is Evidence Typically Authenticated?
There are several common ways to meet this low bar. The most straightforward is witness testimony. If someone saw the item, handled it, or knows it well, their word often does the job.
For example: an officer testifies, "This is the photograph I took at the scene. I remember the angle, the broken streetlight, and the jacket the suspect was wearing." That’s enough. In State v. Thompson, a photo of a defendant was authenticated simply because the officer who took it said, "That’s him." No expert. No lab report. Just a person who was there.
Same with text messages. In State v. Gray, two people testified they received messages from the defendant. A detective testified he took screenshots of those messages. That was enough. The court didn’t need to verify the phone’s IMEI or trace the IP address. The testimony of people who interacted with the messages was sufficient.
Another method is through distinctive characteristics. You don’t need a witness if the item itself gives clues. A letter with a unique handwriting style. A ring with a custom engraving. A document with a watermark, specific font, or header only one company uses. If the item’s appearance, content, or structure points unmistakably to its origin, that’s authentication.
For instance, a threatening note found in a suspect’s locker with the same misspelled word as another note he wrote? That’s enough. The jury can see the pattern. The court doesn’t need a handwriting expert.
What About Handwriting and Signatures?
Rule 901(b)(3) lets the judge or jury compare handwriting samples themselves. You don’t need an expert. Just give them two things: a known sample (say, a signed form from the defendant’s job application) and the disputed one (a threatening letter). Let them look. If they think they match, that’s authentication.
In State v. LeDuc, the court allowed the jury to compare signatures without any forensic analyst. The defendant signed his name on a police form. The prosecution showed a letter with a similar signature. The jury decided they were the same. The court upheld it. No fancy tools. Just human eyes.
What About Old Documents?
If something is old, and it’s been kept where it should be, it’s often considered authenticated by age alone. Rule 901(b)(5) says: if a document or digital file is at least 20 years old, in a place where it would normally be stored, and shows no signs of tampering or suspicion, it’s authenticated.
Think of a 1998 contract found in a company’s archived file cabinet. No one signed it under oath. No one testified about it. But it’s in the right place. It looks old. The paper is yellowed. The ink is faded. The formatting matches 1990s business practices. That’s enough. The law assumes time and proper storage create reliability.

What About Digital Evidence?
Digital evidence-texts, emails, surveillance footage, server logs-has become the norm. And it’s often authenticated through process or system testimony (Rule 901(b)(9)).
You don’t need to prove the system is flawless. You just need to show it works reliably. For example: a cybersecurity analyst says, "This server log comes from our NMCI system. The system automatically timestamps all activity, logs user IDs, and prevents edits. I’ve used it for five years. It’s never failed." That’s enough. The court doesn’t need to audit the code. Just a credible person who knows how the system works.
In military courts, this has been used to authenticate emails, chat logs, and network activity. The key is consistency. If the data matches known patterns-like a user’s login name, device ID, or time zone-it’s likely authentic.
What About Fungible Evidence?
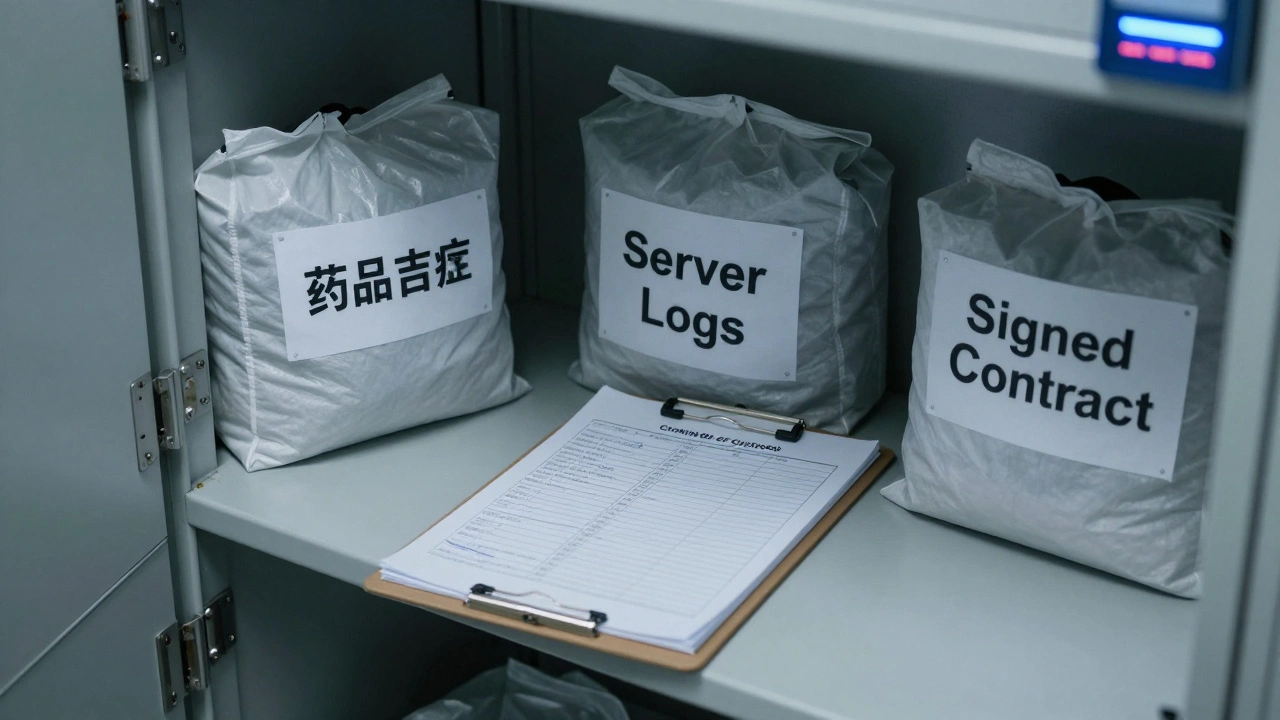
Not all evidence is unique. A bag of white powder. A vial of blood. A dollar bill with a serial number. These are fungible-they can be swapped, mixed, or replaced. For these, you need a chain of custody.
Chain of custody isn’t about proving the item’s truth. It’s about proving it wasn’t switched. Who collected it? Who stored it? Who transported it? Who tested it? Each person must sign or log their handling. Breaks in the chain raise questions. No break? Then it’s authenticated.
For example, if a drug evidence bag was collected by Officer A, logged into evidence locker B, transferred to Lab C, and tested by Analyst D-with no gaps or unexplained gaps-the chain holds. If the log says the bag was left unattended for 12 hours? That’s a problem. The defense can argue contamination or substitution.
What Is Self-Authenticating Evidence?
Some items skip authentication entirely. These are called self-authenticating. Under Rule 901(b)(7)-(10), certain documents don’t need a witness. They come with built-in proof.
Examples include:
- Certified public records (like a birth certificate stamped by a clerk)
- Official government publications
- Published newspapers or periodicals
- Certified business records (like payroll logs stamped by an authorized officer)
- Certified electronic records (like a bank transaction log from a trusted system)
These don’t need a witness because the certification process itself acts as authentication. A notary seal. A government stamp. A digital signature from a trusted system. That’s the proof.
But here’s the catch: self-authenticating doesn’t mean admissible. A certified bank record can still be excluded if it’s irrelevant, misleading, or unfairly prejudicial. Authentication is just the first step.
Authentication vs. Admissibility
It’s easy to confuse authentication with admissibility. They’re not the same.
Authentication says: "Is this what you say it is?"
Admissibility says: "Should this even be shown to the jury?"
Something can be perfectly authenticated-say, a video of a fight-but still be thrown out because it’s too graphic, or it’s hearsay, or it violates privacy rights. Authentication is a door. It doesn’t guarantee you get to walk through every room.
Think of it this way: you authenticate a gun as belonging to the suspect. That’s step one. But if the gun was seized without a warrant, it might still be excluded under the Fourth Amendment. Authentication doesn’t override other rules.
Why Does This Matter in Real Cases?
Without authentication, evidence vanishes. In one 2023 case in Oregon, a prosecutor tried to introduce a video from a security camera. But no one could say where it came from. The store owner didn’t know who maintained the system. The file had no metadata. The defense moved to exclude it. The judge agreed. The video was out. The case collapsed.
On the flip side, in a 2024 fraud case in Wisconsin, the defense tried to challenge a signed contract. The plaintiff didn’t have the signer on the stand. But the contract had a unique logo, a matching watermark, and the same font as other verified documents from the company. The court admitted it. The jury believed it. The defendant was convicted.
Authentication isn’t glamorous. It’s not flashy. But it’s the foundation. Skip it, and your strongest evidence gets tossed. Nail it, and you open the door to the whole case.
What Happens If Authentication Fails?
If the judge rules the evidence isn’t authenticated, it’s excluded. No second chances. No "we’ll try again later." The jury never sees it. That can be fatal to a case.
That’s why lawyers spend hours before trial preparing authentication. They know: if the evidence doesn’t clear this hurdle, nothing else matters.
So whether you’re a prosecutor, defense attorney, or even a witness-you need to know: how do you prove this thing is real? What’s your method? Who will say so? What’s the backup? Because in court, if you can’t answer that, your evidence doesn’t exist.
What is the difference between authentication and verification?
Authentication asks: "Is this what you say it is?" Verification asks: "Is this true?" Authentication is a legal gate-just enough to let evidence in. Verification is what the jury does after it’s admitted-deciding if it’s actually true. One is procedural. The other is substantive.
Can evidence be authenticated without a witness?
Yes. Evidence can be authenticated by its distinctive characteristics, age, or through certification. A 25-year-old contract found in a safe, a certified public record with an official seal, or a digital file with a trusted timestamp can all be authenticated without anyone testifying. The item itself provides the proof.
Do I need a forensic expert to authenticate digital evidence?
No. While experts help, they’re not required. A person familiar with the system-like a network administrator who says, "This email came from our server, and our system logs user IDs automatically,"-can authenticate it. The law allows non-experts to testify about systems they use daily.
What happens if the chain of custody is broken?
A broken chain doesn’t automatically exclude evidence, but it creates reasonable doubt. The defense can argue the item was switched, contaminated, or tampered with. The prosecution must explain the gap. If they can’t, the judge may exclude it-or the jury may dismiss it entirely.
Are all digital files self-authenticating?
No. Only certified digital records-like those stamped by a trusted system, with a digital signature, and properly stored-qualify as self-authenticating. A random file downloaded from the internet, or an unverified screenshot, is not. It still needs authentication through testimony or distinctive traits.





