Imagine a high-stakes courtroom drama where a piece of evidence-perhaps a blood-stained shirt or a decrypted hard drive-is the key to a conviction. The lawyer stands up, presents the item, and the defense attorney asks one simple question: "Where was this item between Tuesday at 2:00 PM and Wednesday at 10:00 AM?" If the prosecution can't answer that with a precise timestamp, the judge might toss the evidence out entirely. It doesn't matter if the evidence is a "smoking gun"; if the timeline is broken, the evidence is useless. This is why chain of custody documentation is the backbone of any legal proceeding.
At its core, time and date documentation is the chronological diary of a piece of evidence. It isn't just about writing down a date; it's about creating a verifiable, unbroken timeline from the second an item is bagged at a crime scene to the moment it's presented in court. If there's a gap-even a small one-it opens the door for claims of tampering, contamination, or mishandling. To keep evidence admissible, you need a record that leaves no room for doubt.
The First Link: Initial Collection
The clock starts the moment an investigator discovers a piece of evidence. In the field, the baseline is established. You can't just jot down "Monday"; you need the exact date and the precise time of collection. This initial entry is the anchor for every subsequent movement of the item. If the start time is wrong, the entire chronological record is skewed.
When collecting evidence, a professional doesn't just record the time. They tie that timestamp to a specific location and a specific person. For example, if a forensic technician collects a mobile phone from a bedside table at 3:14 AM on April 12th, that specific moment is logged. This prevents the "window of opportunity" for a defense lawyer to argue that the device was accessed or altered before it was officially seized.
Managing the Hand-Off: Transfers and Receipts
Evidence rarely stays with one person. It moves from the scene to a transport vehicle, then to an evidence locker, and eventually to a lab analyst. Every single one of these transitions is a high-risk point. This is where most chain of custody failures happen.
A proper transfer record acts like a travelogue. Every time the evidence changes hands, the documentation must capture:
- The exact date and time of the transfer.
- The specific location where the exchange happened.
- The identity of the person releasing the evidence.
- The identity of the person receiving the evidence.
- The reason for the move (e.g., "Transport to State Lab for Toxicology").
Think of it as a relay race. If the baton is dropped, or if we don't know who held the baton for ten minutes during the race, the result is void. Digital signatures have made this process faster, but the rule remains: you cannot erase or "white-out" errors. If a mistake is made in the timestamp, it must be corrected with a transparent note, not deleted, to maintain the integrity of the record.
| Feature | Paper-Based Logs | Digital Log Systems |
|---|---|---|
| Timestamp Precision | Manual (Prone to rounding) | Automatic (Millisecond precision) |
| Audit Trail | Physical signatures | Digital footprints/User logs |
| Error Correction | Cross-outs (Visible) | Version history/Append-only logs |
| Retrieval Speed | Slow (Manual searching) | Instant (Database query) |
Storage, Access, and Modifications
Just because evidence is sitting in a secure locker doesn't mean the documentation stops. Any interaction with the evidence while in storage must be logged. If a detective retrieves a sample for a second look, the log must show exactly when it left the locker and when it returned.
A critical but often overlooked area is the modification of evidence. In many cases, evidence is altered for analysis-like a blood sample being split into two vials for testing. This is not "tampering," but it is a change. Every sample taken must have its own timestamp. If a lab technician opens a sealed bag at 10:00 AM and extracts a swab at 10:15 AM, those fifteen minutes are a vital part of the record. Without these specific times, a lawyer could argue that the sample was contaminated during an undocumented period of exposure.

The Digital Evidence Challenge
Digital evidence brings a whole new level of complexity. Unlike a physical weapon, digital data can be changed in a fraction of a second without leaving a visible mark. Here, the chain of custody must span from the first bit of data captured to the moment it's projected on a courtroom screen.
In digital forensics, timestamps are everything. Metadata-the "data about the data"-contains creation and modification dates that can prove a file was altered after a crime occurred. However, if the investigator fails to document the time they imaged a drive, or if they accidentally change the system clock on the forensic workstation, the metadata becomes suspect. To avoid this, experts use write-blockers to ensure no data is changed and meticulously log the start and end times of every imaging process.
If a digital log is incomplete, the evidence can be rendered inadmissible. It doesn't matter if the file contains a clear confession; if the timestamps associated with the collection are missing or contradictory, the court cannot verify that the evidence is an authentic representation of what was on the device at the time of seizure.
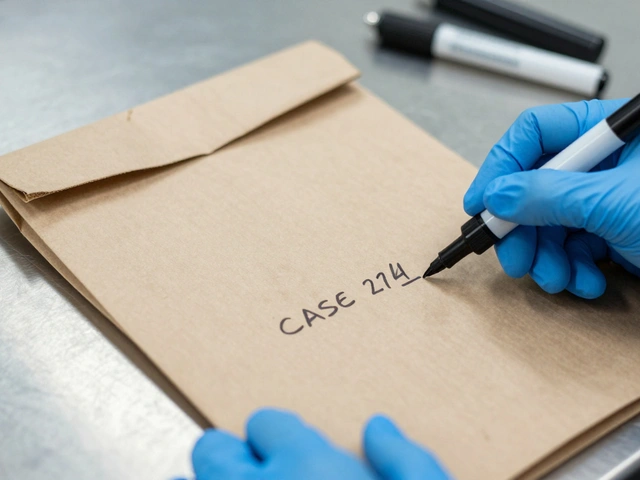
Using Unique Identifiers for Precision
Time and date stamps don't work in a vacuum; they need a target. This is where unique identifiers come in. Every piece of evidence is assigned a specific case number and exhibit number (e.g., Case #2026-452, Exhibit B). By pairing a unique ID with a timestamp, you create a precise coordinate in time and space.
When an investigator records "Exhibit B moved to Lab A at 2:00 PM," the unique identifier ensures there is no confusion with "Exhibit C," which might have been moved at the same time. This combination allows the prosecution and defense to cross-reference the travelogue of the evidence against the logs of the facility, ensuring that the item in the courtroom is exactly the item collected at the scene.

The High Cost of Sloppy Record Keeping
What happens when the documentation fails? The legal implications are severe. Courts operate on the principle of authenticity. If the chronological record is broken-meaning there is a period where the evidence's location and handler are unknown-the chain is considered "broken."
A broken chain of custody can lead to the total exclusion of evidence. Imagine a case where a forensic lab has the perfect DNA match, but the log shows the evidence was "unaccounted for" for four hours during a transfer between agencies. The defense will argue that the sample could have been swapped or contaminated during those four hours. Even if the lab can prove the DNA is correct, the lack of a temporal record makes the evidence legally unreliable. In the eyes of the law, an undocumented moment is a compromised moment.
Can a digital signature replace a physical one in a chain of custody log?
Yes, digital signatures are widely accepted, provided the system used to capture them is secure and creates an unalterable audit trail. The most critical requirement is that no erroneous information can be erased or overwritten without a recorded correction, ensuring the integrity of the chronological record remains intact.
How long must chain of custody documentation be kept?
Generally, the documentation must be maintained for at least as long as the court is considering the evidence. This often extends through the entire duration of the trial and any subsequent appeals process to ensure the authenticity of the evidence can be challenged or verified at any time.
What is the difference between a timestamp and a date in these logs?
A date provides the calendar day, but a timestamp provides the specific hour, minute, and sometimes second. In legal proceedings, a date is often insufficient because the window between 8:00 AM and 5:00 PM is large enough for evidence to be mishandled. Timestamps provide the granular precision needed to prove an unbroken chain.
Does the chain of custody apply to digital copies of evidence?
Absolutely. The chain starts from the first point of data collection, including the creation of forensic images (copies). The process of hashing the data-creating a unique digital fingerprint-is paired with a timestamp to prove that the copy has not been altered since the moment it was created.
What should an investigator do if they realize they forgot to log a transfer time?
The investigator should never attempt to "guess" or forge the time. Instead, they should make a supplemental entry as soon as the error is discovered, explaining the gap and providing the best available information to reconstruct the timeline. Transparency is better than a perceived cover-up, though the gap may still be challenged in court.
Next Steps for Maintaining Integrity
Whether you are a field agent or a lab technician, the goal is the same: eliminate doubt. To do this, lean on a few simple rules. First, record the time immediately-don't wait until you get back to the station. Second, be specific; "approximately 2 PM" is a weakness that a defense attorney will exploit. Use "14:02." Third, ensure every hand-off is a two-way street where both the giver and receiver sign and timestamp the document.
If you are managing a team, consider moving toward digital evidence management systems that automate timestamps. This removes human error from the equation and provides an instant, searchable audit trail. By treating the time and date as being just as important as the evidence itself, you ensure that the truth found in the lab actually makes it to the verdict.