When a crime goes unsolved for years-sometimes decades-the evidence doesn’t just sit quietly. It waits. And in today’s world, that evidence is often digital. A forgotten USB drive. A cracked phone buried in an evidence locker. A VHS tape labeled "Case 1997-042". These aren’t relics. They’re time capsules. And with the right tools, they can crack open cases thought dead forever.
Why Digital Evidence Outlasts Physical Evidence
Physical evidence degrades. Blood stains fade. Fibers crumble. Fingerprints vanish from surfaces. But digital data? It doesn’t rot. A hard drive stored in a climate-controlled vault can hold perfect copies of files from 20 years ago. The problem isn’t the data-it’s the tools to read it. In the early 2000s, investigators couldn’t access encrypted phones. They didn’t know where to look for deleted messages. Cloud backups? Nonexistent. Today, forensic tools can pull data from devices that were locked, wiped, or even physically damaged. What was impossible in 2005 is routine in 2026. That’s why cold cases are being solved now-not because new witnesses came forward, but because old devices finally talked.The Hidden Life of Legacy Devices
Think of your smartphone. You delete a photo. You factory reset it. You think it’s gone. But forensic software can still find traces: cached thumbnails, temporary files, app usage logs, GPS pings from apps you haven’t opened in years. These are called system artifacts. They’re the digital breadcrumbs left behind by every tap, swipe, and search. Take a 2012 iPhone. Back then, iOS didn’t encrypt the entire drive until after the first unlock. If the device was seized while still powered on, investigators got full access. But if it died in storage? The encryption reset. No data. No chance. Today’s tools can bypass that. They can restore the state of the device as if it had never lost power. That means a phone seized in 2013 can now yield location history, call logs, and even deleted texts from 2012. And it’s not just phones. Old laptops, MP3 players, digital cameras, even GPS trackers from police cruisers-each holds pieces of a puzzle no one knew was missing.How the Green River Killer Was Caught
The Green River Killer case spanned over 20 years. At least 49 women were murdered in Washington State. Suspects were questioned. Leads went cold. Physical evidence was stored, but no one could connect it. In 2001, investigators began digitizing old evidence: photos, autopsy reports, witness statements. They scanned documents, uploaded them into a centralized system, and tagged everything. Then came the breakthrough: DNA from a crime scene sample was retested using newer techniques. It matched Gary Ridgway-but he’d already been interviewed. Why wasn’t he charged? Because the old case files didn’t link his name to the DNA sample. The digital system did. Once the data was searchable, investigators pulled up every file with Ridgway’s name. They found a single handwritten note from a 1984 interview: "He mentioned he worked at a truck yard near the river." That detail had been buried in a paper folder. In the digital system? It popped up in seconds. Ridgway confessed. Without digitization and digital forensics, he might still be free.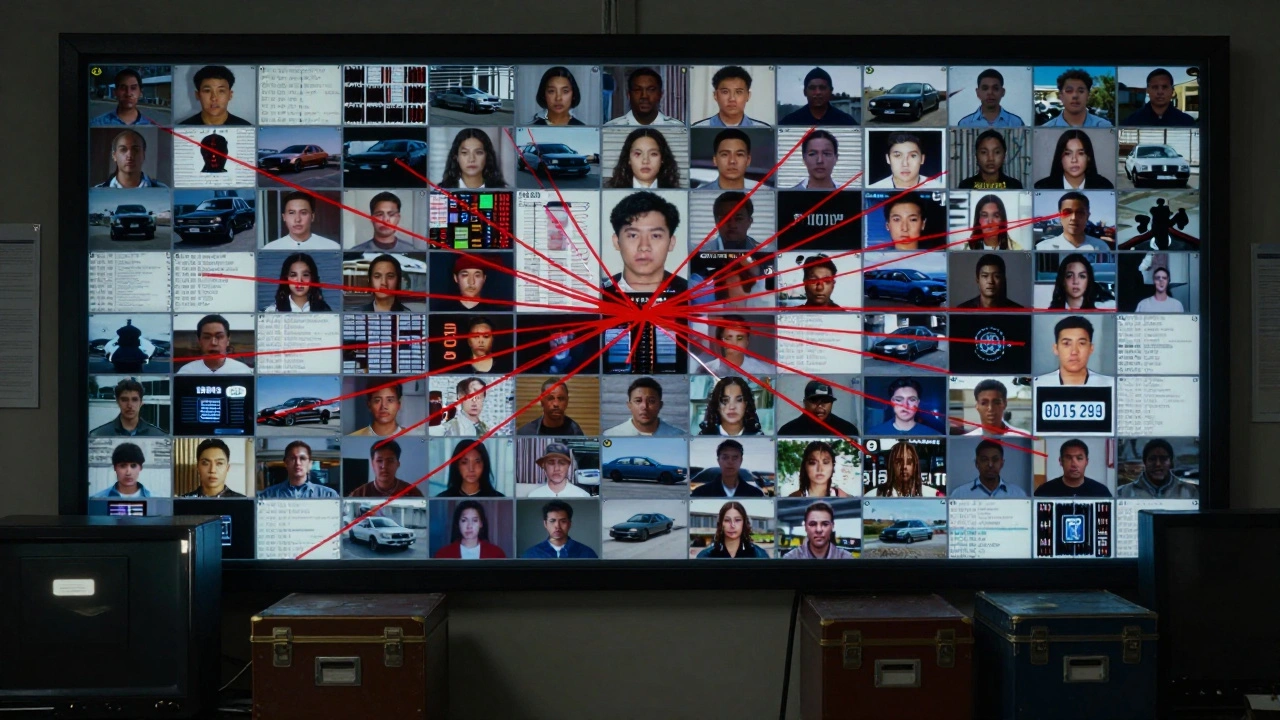
The Power of Evidence Management Systems
Modern cold case units don’t just store evidence. They organize it. Systems like those used by the LAPD and NCMEC let investigators search across hundreds of cases using keywords, facial recognition, DNA profiles, or even vehicle license plates. In 2018, investigators re-examined a 1992 homicide using one such system. They uploaded DNA files from the victim’s clothing. The software cross-referenced them with every other unsolved case in the state. It flagged a match from a 1995 abduction in another county. The suspect? Joseph James DeAngelo-the Golden State Killer. He had never been a suspect in the 1992 case. The connection was invisible until software compared DNA across decades. That’s not luck. That’s methodology. These systems don’t just store files. They create relationships. A photo from a 1999 missing person case might show a car in the background. Another case from 2003 has a similar car in a different photo. AI tools can now compare those images, analyze lighting, and suggest they’re the same vehicle. That’s a lead. A real one.Why You Can’t Just Archive and Forget
Storing old devices isn’t enough. If you shut off a phone and leave it in a drawer for ten years, you lose access to its data. Modern encryption works differently than it used to. Many devices now wipe their decryption keys if they lose power. That’s why agencies now have active storage protocols:- Devices are kept on trickle-charging stations to maintain power
- Forensic images are made and stored in the cloud with checksum verification
- Each device’s make, model, OS version, and acquisition type are logged
- Every six months, tech teams check new tool updates against the log

Where the Real Breakthroughs Happen
The biggest gains in cold case forensics aren’t from flashy AI or genealogy databases. They’re from the mundane: re-examining what was already collected. Most cases aren’t solved because of new evidence. They’re solved because old evidence was looked at again-with better tools. A 2015 Android phone seized in a 2017 murder case had a corrupted SD card. Back then, it was labeled "unrecoverable." In 2024, a forensic lab used a new chip-off technique to read the memory directly. They found 17 deleted photos. One showed the suspect standing next to the victim’s car. Another showed a license plate. That plate led to a rental record. That record led to a confession. It wasn’t a breakthrough in technology. It was a breakthrough in patience. In discipline. In knowing that today’s tool might unlock yesterday’s secret.The Future Isn’t Just About New Tools-It’s About New Habits
The most successful cold case units don’t wait for a case to go cold. They build systems to keep evidence alive:- All evidence is digitized at intake: photos, documents, audio, even physical items scanned in 3D
- Every item is tagged with metadata: who collected it, when, where, and why
- Access logs track every time a file is opened or copied
- Annual reviews are mandatory: every cold case file gets re-run through updated software





